How .ICS Attachments Become Malicious
Next time you’re invited to a meeting, plan on being late – unless you want to give hackers access to your computer, network, or entire IT system. In the ongoing and ever-evolving battle against hackers, it’s come down to this: even responding to a meeting invitation can give hackers the in that they need to wreak digital havoc on your business. How? Through .ICS attachments.
Let’s dig into what .ICS attachments are, how hackers are able to exploit them, and how Votiro can ensure your organization stays proactive.
What is an .ICS File?
.ICS files were introduced in 1998, and they are different from email invitations in that they push themselves into calendar apps. .ICS attachments are one of the few file formats that are capable of doing that – and the fact that they are common to major calendar apps on all platforms gives hackers an extra edge in spreading malware. All it takes is one contaminated invitation, and you can infect a whole company.
So, how can a simple meeting invite become malicious? Unfortunately, hackers have found a way to use a new twist on an old exploit to carry out DDE attacks, in which Microsoft allows two running applications to share the same data. This particular vulnerability is based on .ICS attachments, and the DDE protocol hackers are exploiting can be used by applications for both one-time data transfers and for continuous exchanges in which apps send updates to one another as new data becomes available. Thousands of applications use the DDE protocol, including Microsoft’s Excel, MS Word, Quattro Pro, and Visual Basic. New research also indicates that hackers are now using .ICS files to hook into applications and to carry out zero-footprint attacks that are essentially undetectable to standard security systems.
How Hackers Exploit .ICS Attachments
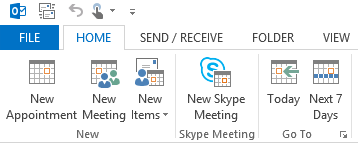
Of course, .ICS attachments work with Outlook as well, and unlike regular email messages that land in your inbox and require viewing them, Outlook automatically inserts .ICS messages into your calendar as “tentative.” Often, invitations incorporate attachments (Base64 encoded binary data) to make them more meaningful. Once an invitation is accepted, that attachment, with its malware-laden payload, gets its chance at installation. Besides attachments, malicious .ICS files can include links to external files (URI option) that could install malware when clicked on. When an invitation is passed on, the malware or malicious link is passed on as well – infecting others down the line.
As anti-virus programs don’t address .ICS files, it would be a relatively simple matter for hackers to pass their goods on using this method. This trick has actually been in use for years, but in the past, it was generally used to pass spam. Now, with the hooks into MS applications (such as attaching a Word file with a poison macro to the .ICS invitation), hackers have increasingly begun to use this method to carry out attacks.
Steering Clear of Malicious .ICS Files with Votiro
So does that mean the end of meetings? Not at all. With Votiro, the .ICS DDE threat is moot. Using our Positive Selection® technology, files are broken down into their distinct components, and anything that doesn’t match a file’s specification is removed. In the case of .ICS files, the file would be analyzed in its separate components, and if anything is amiss – such as excess or non-standard code in a file attached to an invitation – it gets removed. The invitation, together with its file, is reconstructed and passed onto its recipient. This process is known as file sanitization, and it works like a charm against malicious .ICS attachments.
Antivirus programs can’t ensure your organization stays free from these threats, and all the best sandboxes can do is arrest the .ICS invitation altogether (if there is a rule for that), making .ICS files useless. The point of .ICS is to be able to install invitations in a calendar automatically. If the invitations don’t get to the recipient as a calendar file, there’s no point in sending it. With Votiro, users are protected – and the flow of business is uninterrupted. When your organization implements our technology, invitations are once again something to be anticipated, not feared.
News you can use
Stay up-to-date on the latest industry news and get all the insights you need to navigate the cybersecurity world like a pro. It's as easy as using that form to the right. No catch. Just click, fill, subscribe, and sit back as the information comes to you.
Sign-up Here!
Subscribe to our newsletter for real-time insights about the cybersecurity industry.



