Resource
Center
News You Can Use
Stay up-to-date on the latest industry news, plus get all the insights you need to navigate the cybersecurity world like a pro.
All Resources
CVE-2025-50165: This Windows JPEG Vulnerability Proves Detection Isn’t Enough

How to Enable Safe File Handling for Clinical and Research Portals

Inside the Ingram Micro Ransomware Attack: Lessons in Zero Trust
Closing the Zero Trust Loop: ZTNA + CDR

The Usual Suspects: 9 Dangerous File Types Every CISO Should Know

When the Patches Stop: Protecting Your (Windows 10) Environment with CDR

One Policy for Every File
6 Business Workflows Where Files Create Risk & How to Secure Them

How Votiro Turns Threat Prevention Into Intelligence
The 8 Most Dangerous File Types for Malware Infections

How File Sanitization (aka CDR) Protects Supply Chain Data

5 Everyday File Uses That Add Business Risk & How to Secure Them

The Case for Frictionless File Protection

10 File Threats That Slip Past Traditional Security—and How to Stop Them
True Threat Prevention Demands Browser Security & File Sanitization
7 Ways False Positives Drain the SOC + How to Eliminate Them

Why File Sanitization for Retail Matters

How to Stay Ahead of Data Privacy Regulations in 4 Key Regions
10 Questions CISOs Should Be Asking About File Security

CDR for Credit Unions: Stronger Security, Faster Service, Easier Compliance
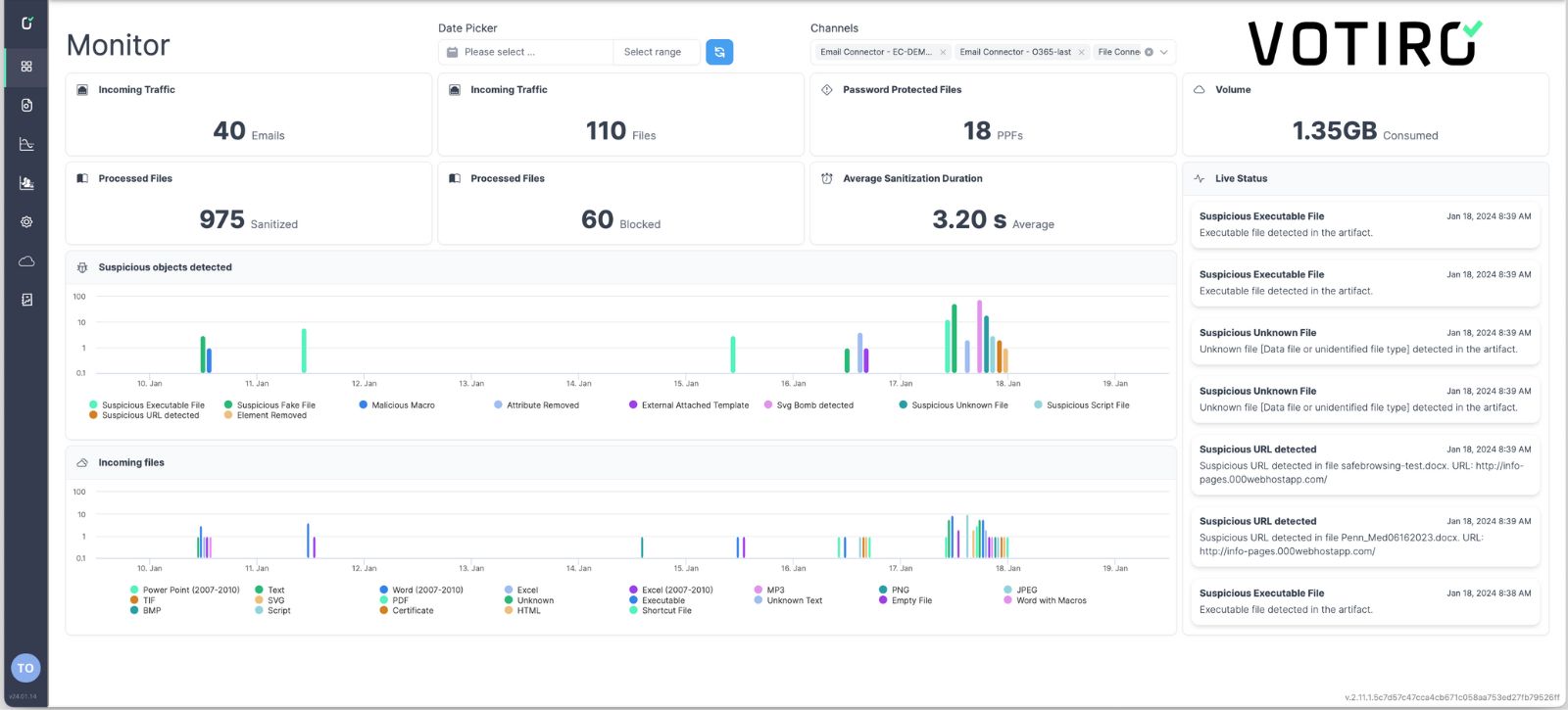
See Votiro DDR in Action
Book a live demo to see how Votiro Data Detection and Response can keep your organization safe and compliant with real-time data masking and proactive malware prevention.