Healthcare Industry
Votiro for
Healthcare Cybersecurity.
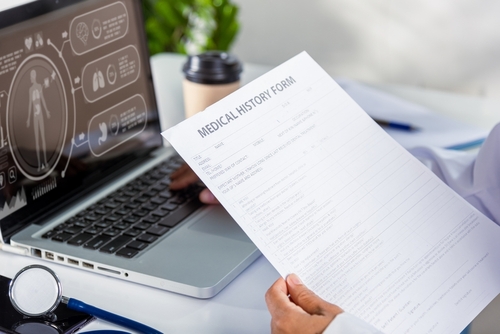
There are major financial incentives for cyber attacks to target the healthcare and health insurance industries – it’s a seller’s black market for financial data and medical information. And while greater digital accessibility has improved services and enabled more efficient cross-organization communication, it has also increased exposure to data security threats — via private data exfiltration and hidden malware.
What the healthcare industry needs is a modern data security solution. Enter Votiro.
Patient data is privileged. Votiro keeps it that way.
Why Votiro is Perfect for Cybersecurity in Healthcare

Votiro eliminates file-borne risks to the healthcare industry.
Healthcare facilities are 24/7 machines that ingest countless documents from third-parties and other providers, including some of the most private information available – patient data. The risk associated with handling such a large volume of files is immense, leaving hospitals a prime source for cyber attacks as teams transfer and receive data from multiple sources, like email, FTP, web portals, and other methods of file exchange.
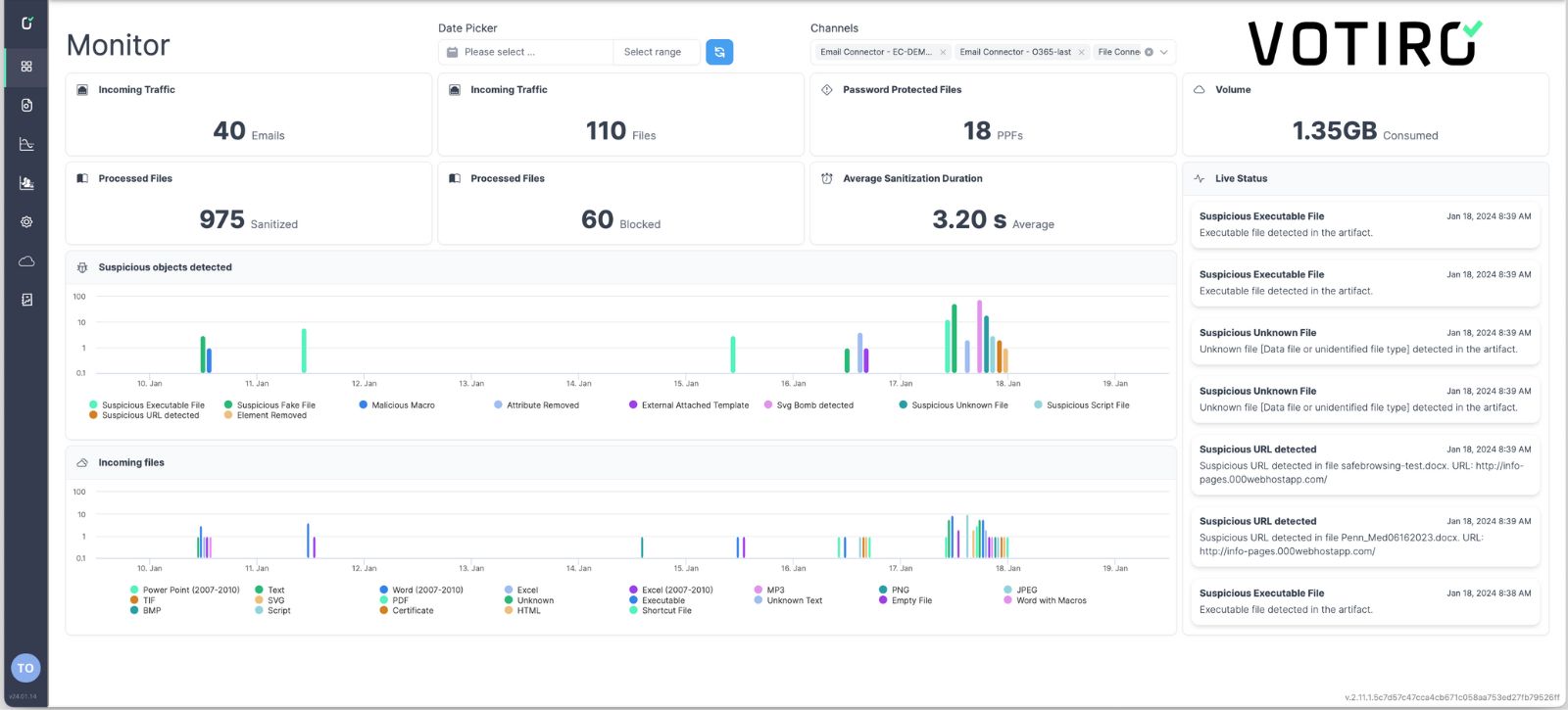
With Votiro’s Zero Trust Data Detection & Response (DDR), all incoming files are cleansed of threats before they reach organizational endpoints – including the ability to mask private data in real-time. This allows healthcare providers to remain compliant with PHI, HIPAA, and other regulations while ensuring that employees are opening safe content and that systems aren’t ingesting malware by mistake.
Real-time privacy to keep patient data secure, and providers compliant.
Although regulations like HIPAA are in place to protect medical information from unauthorized access, this doesn’t prevent cyber criminals from infiltrating your environment and exposing data via ransomware. Even without a threat actor in play, healthcare regulations cannot prevent the accidental sharing of confidential information without a proactive data security solution in place.
That’s why Votiro tackles both sides of the data security problem by preventing malware threats and privacy risks at the same time. So, while many so-called solutions can only flag sensitive information for follow-up or respond to data breaches after-the-fact, Votiro mitigates potential harm in real-time.
See Votiro DDR in Action
Book a live demo to see how Votiro Data Detection and Response can keep your organization safe and compliant with real-time data masking and proactive malware prevention.