Votiro for
Email Security
Secure every email from malicious content and ensure file attachments are safe to enter your organization.
As an essential part of the workplace, most employees use email without thinking twice about the hidden threats that can make their way in. Hackers easily exploit this by targeting employees with malicious elements hidden within body copy and attachments when they least suspect it.
While email continues to be a primary target for malware, current solutions aren’t designed to catch every threat, leaving entire organizations just one click away from disaster. That is, unless they have Votiro.
Secure Email Engagement
How Votiro Works
- An external contact will send phishing emails to your employees with malicious attachments and URLs.
- Votiro breaks the email down to its base components, separating text, urls, images, attachments, and everything in between.
- Votiro starts building a new email using only the elements that were found to be 100% secure — anything that was known or could have been malicious is left behind.
- Your employees receive safe emails with potentially malicious attachments or URLs left behind.
Data security so good, you won’t even know Votiro is there.
 Why Votiro for your email security?
Why Votiro for your email security?
Zero training required
Seamless integrations with everything
Works in cloud and on-premise
Implementation in as fast as 10 minutes
Stop malicious attachments from ruining your email experience.
Today’s cybersecurity solutions simply aren’t enough to protect your team from malware hidden in emails and their file attachments. Unfortunately, current solutions like antivirus are not able to keep up with advanced threats and zero-day exploits, leaving you with large gaps that can compromise entire networks and open you up to sensitive data breaches.
With Votiro’s deep understanding in file composition and weaponization, our Zero Trust approach to file security extends seamlessly to that of the email ecosystem. With Votiro, your emails will no longer pose a threat to your business.

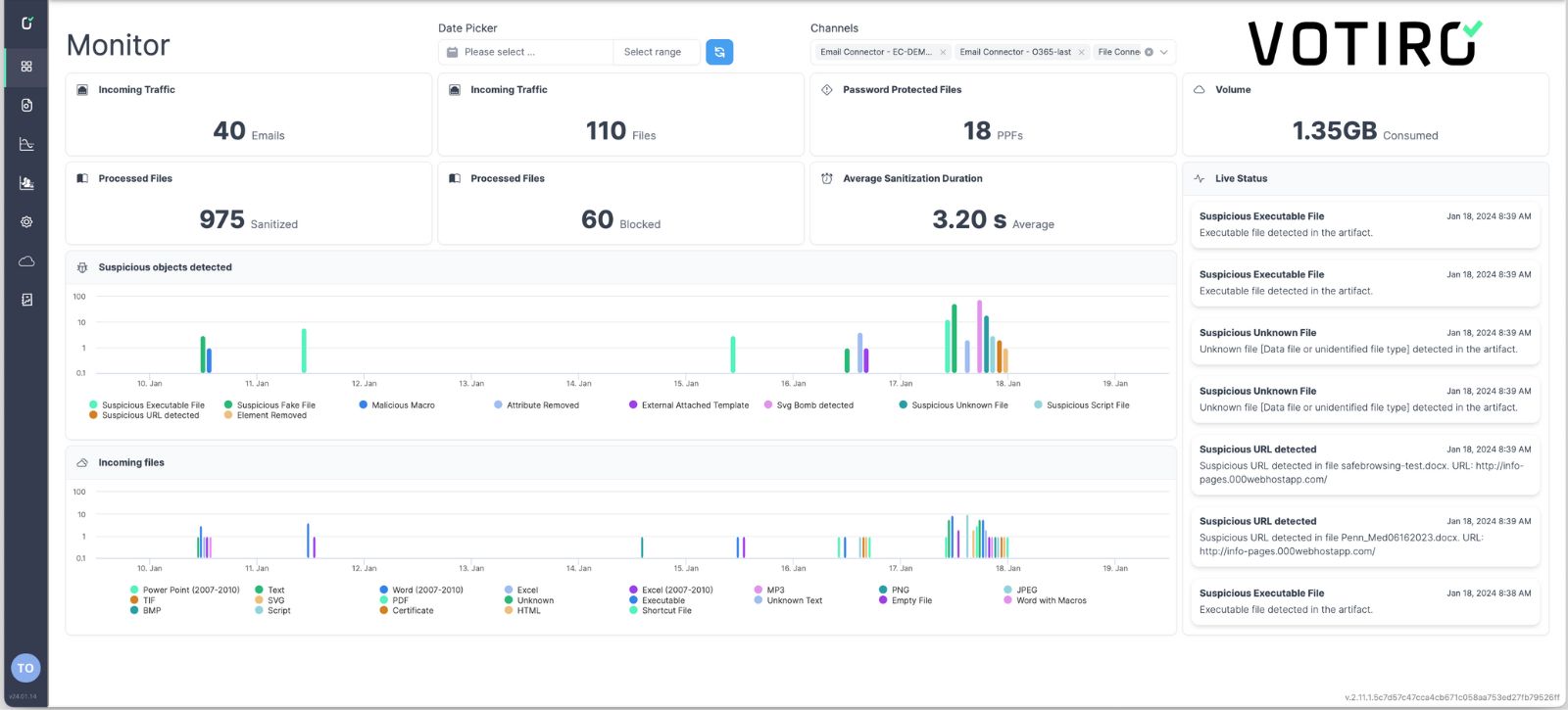
See Votiro DDR in Action
Book a live demo to see how Votiro Data Detection and Response can keep your organization safe and compliant with real-time data masking and proactive malware prevention.