Resource
Center
News You Can Use
Stay up-to-date on the latest industry news, plus get all the insights you need to navigate the cybersecurity world like a pro.
All Resources

Why You Should Simplify Your Cybersecurity Tech Stack

Guide: Ensuring Private Data Protection & Compliance

The Guide to Zero Trust Data Detection & Response (DDR)

The Meme-Guide to Security Compliance for Financial Institutions

Integrating Votiro into Your Existing Security Architecture

2023 Content Security Report

Mitigating the Risk of Armed Content within the Enterprise

The Security Architect’s Guide to File Sanitization

Enterprise ROI Estimate for the Votiro Platform

The Complete Guide to Threats in Files

Content Disarm & Reconstruction (CDR) Buyer’s Guide

2022 Votiro File Error Report
Mitigating File-borne Threats in the Financial Services Industry

14 Lessons Learned for CISOs from a Ransomware Survivor CIO

Ryuk Ransomware & Government Agencies

The Complete Guide to Content Disarm and Reconstruction (CDR)

Malicious Macros: The Holes in Microsoft Software Hackers Hope You Don’t Know About
How to Plug the Gaps in Antivirus, NGAV, and Sandbox File Security
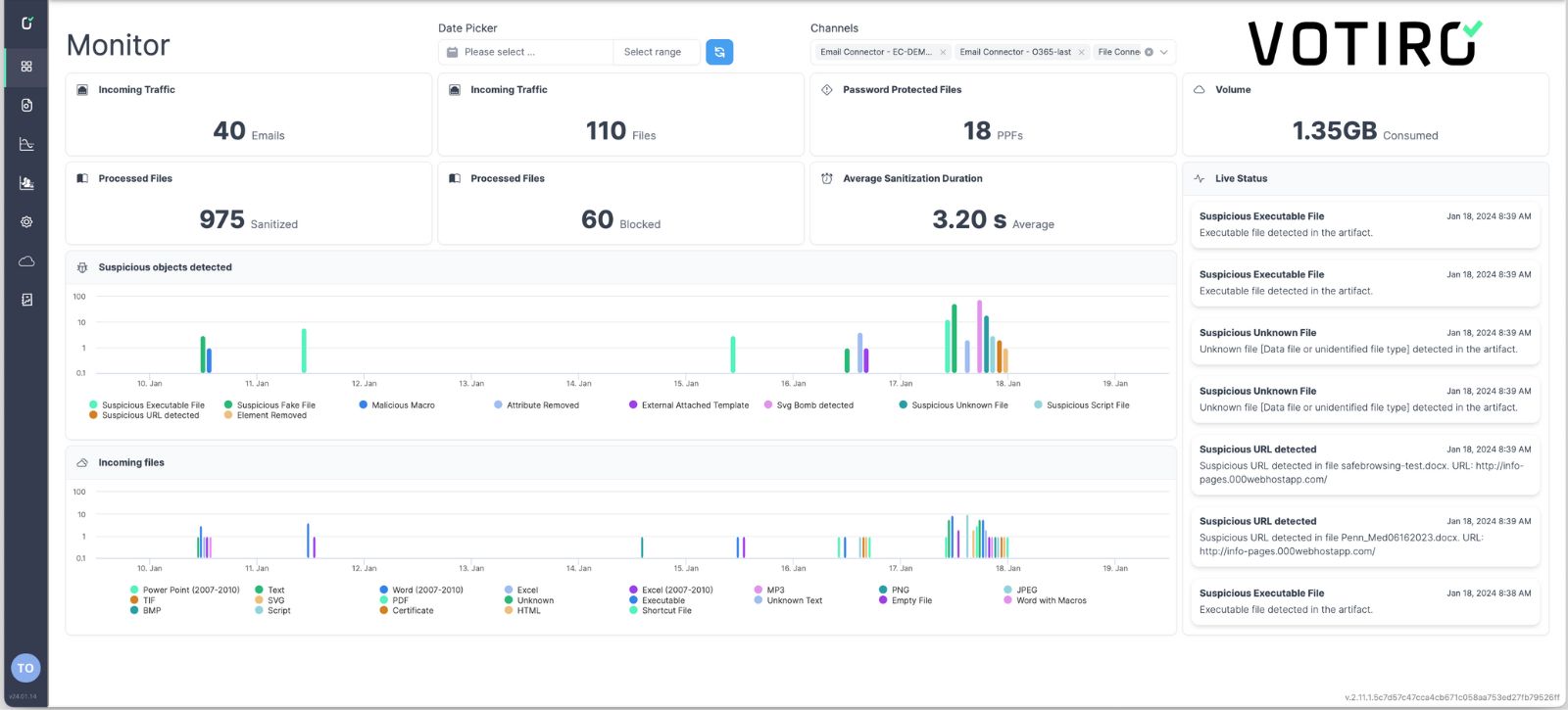
See Votiro DDR in Action
Book a live demo to see how Votiro Data Detection and Response can keep your organization safe and compliant with real-time data masking and proactive malware prevention.
![]()