Structured Data vs. Unstructured Data: How to Safeguard Your Business
Organizations run on the power of their data; from predicting customer behavior to evaluating working processes to managing day-to-day operations. More than just information in a database or data lake, business data exists in many forms, extending throughout all organizational operations, from call centers to the C-suite. This is why the loss of such data through a catastrophic event (such as a ransomware infestation) can devastate a business.
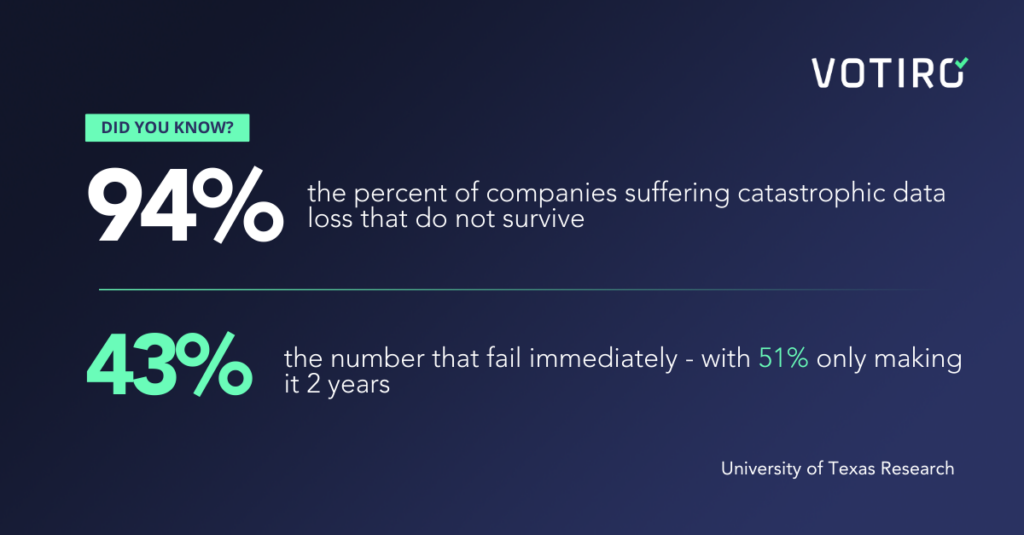
According to University of Texas research, 94% of companies suffering catastrophic data loss do not survive, with 43% failing immediately and 51% only making it 2 years.
This article explores the different types of data that organizations store and provides actionable advice on preventing catastrophic data loss from one of the greatest threats.
What is Structured Data?
Structured data is a cornerstone for data management and operations in business environments. Its high organization and consistent formatting, typically in databases or spreadsheets, facilitate easy entry, search, and analysis. This consistent formatting is often envisioned in the form of tables where each column represents a specific data type, and the rows represent a record.
Common uses for structured data include:
- Business Intelligence, which aids in analyzing customer information, sales patterns, and market trends
- Reporting and Analytics for generating financial reports and performance metrics
- Customer Relationship Management (CRM) for managing customer details
- Inventory Management to track stock and manage supply chains
What is Unstructured Data?
Unstructured data, characterized by its lack of a predefined format or organization, encompasses various information types such as text, images, videos, and social media content. This data comprises most data used in daily business operations, accounting for 80% of the data stored.
These files often come in specific file types with their own formatting and rules for file composition. Unlike structured data, it’s not easily sorted into traditional database fields, making it harder to sort and analyze.
While this data is more varied than structured data, there are still data analysis tools that leverage unstructured data. NoSQL databases can store unstructured data in ways that can be queried, much like a traditional database, but with no fixed formatting. Also, artificial intelligence (AI) and machine learning (ML) algorithms ingest unstructured data as part of their learning to derive insights from the data. With generative AI programs being fed an internet’s worth of unstructured data, it’s easy to see how unstructured data can be leveraged for harm.
Understanding the Differences in Data Types
The most apparent difference between the two types of data is the format, which is highly organized, structured, and unstructured, and is not tied to any specific formatting.
This difference drives how the two are stored:
- Structured data is often stored in databases with a fixed format and set of relations, joining different records by shared attributes, which allows them to be quickly queried. Rather than sharing the database files, the data is first queried before it can be shared.
- Unstructured files, on the other hand, exist in independent files, which can easily be handed off individually, allowing users to share them with little effort.
Data Malware Risks
Despite the differences in the data types and their uses, both are susceptible to malware in different ways. While malware doesn’t directly “infect” the data itself, such as the fields in a database, it does affect the systems that manage, store, and process this data. By infecting these systems, it can gain direct access to the data inside, allowing it to steal, destroy, or alter it.
Such attacks may use encryption to hold the data for ransom or exfiltrate it to the attackers for sale. The structured format of this data makes it easier for malware to scan and analyze the storage for high-value sensitive data, allowing the criminals to most effectively target their attack.
Unstructured data, on the other hand, can be targeted by malware due to its ease of sharing. Malware can be embedded directly in these files, hiding within what appears to be an ordinarily safe format, such as a document or image. When the file is opened, the payload of the hidden malware launches its malicious code. Once launched, the code can launch several payloads, with ransomware, data stealers, rootkits, and keyloggers being some of the most common. After the code has launched, more advanced malware can search out new targets on the network, spreading the infection and infecting structured data storage locations.
Defending All Data
While malware is a threat to all varieties of data, it can still be stopped. Protecting structured data from malware comes from effectively stopping unstructured data from being a vector in the first place. Doing this requires integrating data protection directly into the processes that allow data to cross organizational boundaries.
The most advanced solutions for data defense seamlessly embed themselves as part of the information flow, hiding behind the scenes yet connecting directly to the software tools businesses rely on.
Traditional data protection approaches rely solely on antivirus (AV) to reside on endpoints. This method can effectively stop known threats once they arrive at an endpoint, but has flaws of its own. While AV can stop previously discovered threats, it is unreliable for unknown or zero-day threats. It also relies upon the threat arriving at the endpoint, creating an opportunity for the file to be opened and the payload to launch before the AV has a chance to stop it.
More advanced approaches combine AV with Content Disarm and Reconstruction (CDR) to sanitize data in real-time as it passes through boundaries. Rather than residing on a single endpoint, the data is protected en route, preventing the risk of the payload launching on the endpoint. The CDR enhances the AV to eliminate zero-day and previously unknown threats, gaining the benefits of both technologies. This integration sits behind the scenes, allowing protection without adding friction to users and enabling users to share and collaborate without impeding productivity.
Votiro Protects Data of All Types
Votiro’s Zero Trust Data Detection and Response platform enhances data security for both structured and unstructured data by integrating advanced capabilities including:
- Real-time privacy and compliance to mask private data such as PII, PHI, and PCI in motion and ensure it ends up in the right hands (and out of the wrong ones)
- Proactive threat prevention using Votiro’s CDR technology – dubbed Positive Selection® – to stop unknown, zero-day threats before they reach endpoints
- AV to bolster defenses and complement the CDR capabilities
- RetroScan technology to review and understand previous threats that may be caught when AV systems later recognize threats
This comprehensive strategy positions Votiro as a robust solution against concealed cyber threats, ensuring high-level data protection for organizations.
Contact us today to learn how Votiro sets the bar for protecting your data. And if you’re ready to try Votiro for yourself, you can take a free 30-day trial right here!
News you can use
Stay up-to-date on the latest industry news and get all the insights you need to navigate the cybersecurity world like a pro. It's as easy as using that form to the right. No catch. Just click, fill, subscribe, and sit back as the information comes to you.
Sign-up Here!
Subscribe to our newsletter for real-time insights about the cybersecurity industry.



