How to Avoid CVE-2021-40444 and Secure Employee Files at Scale

Zero-day vulnerabilities by design have always been a thorn in the side of the security team that’s trying to balance allowing employees to continue working productively with ensuring that they are protected from threats while waiting for a patch. Recently, a new zero-day threat was discovered called CVE-2021-40444 that adds risk for any employee that opens a file containing this vulnerability.
Actively and notably exploitable until a patch was released on September 14th, 2021, this threat is an example of the challenge security teams face: should they scramble to turn off legitimate features and functions used in employee day-to-day activities because of a zero-day exploit?
Or should they simply block these files from reaching employees, even if it impacts their work?
Or should they cross their fingers and wait for Patch Tuesday?
Thankfully, for threats delivered via documents like CVE-2021-40444, there is a solution approach called content disarm and reconstruction (CDR) that allows for employees to both be secure and productive.
In this article, we overview the CVE-2021-40444 vulnerability and how Votiro CDR as a service delivers safe files to employees at scale, so that new zero-days and similar new threats don’t disrupt the pace of business.
What is CVE-2021-40444? Explaining the Threat
This threat leverages weaponized Microsoft Office documents to exploit a Windows vulnerability that impacts the currently discontinued Internet Explorer.
According to Microsoft, hackers make use of CVE-2021-40444 to embed a malicious ActiveX control within a Microsoft 365 document. ActiveX is a legitimate function inside of Microsoft Word, Excel, and PowerPoint documents that enables the embedding of online content into these files. However, when a CVE-2021-40444 file is opened, the ActiveX control allows remote code to execute in order to deliver malware payloads, such as Cobalt Strike.
Let’s take a closer look at how CVE-2021-40444 exploits a remote code execution vulnerability, and how Votiro CDR as a service proactively prevents against this threat – as well as any hidden malware or executable – so that employees can continue to use and process documents safely.
Votiro vs. CVE-2021-40444: Putting the Solution to the Test
Security professionals at Votiro ran a live test of the CVE-2021-40444 threat through the Votiro solution.
First, below is a screenshot of the original malicious file in VirusTotal, an independent website that aims to raise the global IT security level through sharing threat information. 33 security vendors flagged the file as malicious.
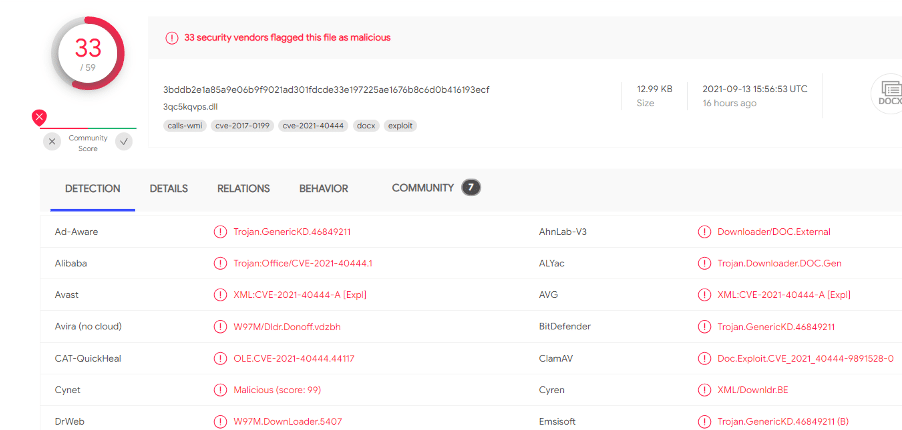
Source: https://www.virustotal.com/gui/file/3bddb2e1a85a9e06b9f9021ad301fdcde33e197225ae1676b8c6d0b416193ecf
Unfortunately, the malicious elements were not detected by several other anti-virus products. Traditional methods using signature-based detection might identify exploitation activity after gathering and extracting several samples, but in the meantime an exploit that a hacker has manipulated will be able to avoid signature detection. This underscores just how inefficient detection can be and the potential impact a single piece of malware can have.
Votiro Content Disarm and Reconstruction (CDR) at Work
Votiro Content Disarm and Reconstruction SaaS powered by a Positive Selection® engine takes a proactive approach to cybersecurity by cleansing potentially malicious code from any files. Votiro does not rely on any detection methods like other anti-malware tools. Instead, the Positive Selection engine assumes all files are malicious and sanitizes them of all unknown, not-known-good elements. This removes any malware and embedded malicious code. Votiro CDR as a service then rebuilds the file, creating a new, clean file that includes the functional elements for users to remain productive and secure at the same time.
With Votiro CDR, files are never flattened, and the usability is preserved, eliminating any adverse business impact felt when active content, such as macros or scripts, is removed from files. Unlike other recursive, time-consuming process, Votiro’s CDR process relies on positive selection, with no reliance on checking signature databases for known threats and no opportunity for zero-day attacks.
Following this file sanitization process, the Votiro team re-submitted the cleansed file to the VirusTotal interface in order to test its effectiveness. “After the internal test with the samples,” Aviv Grafi, CTO said, “we can demonstrate that Votiro removed any external target and the file is disarmed after sanitization.” As seen in the screenshot below, VirusTotal confirmed Votiro’s sanitization was effective with 0 detections of any malicious elements.
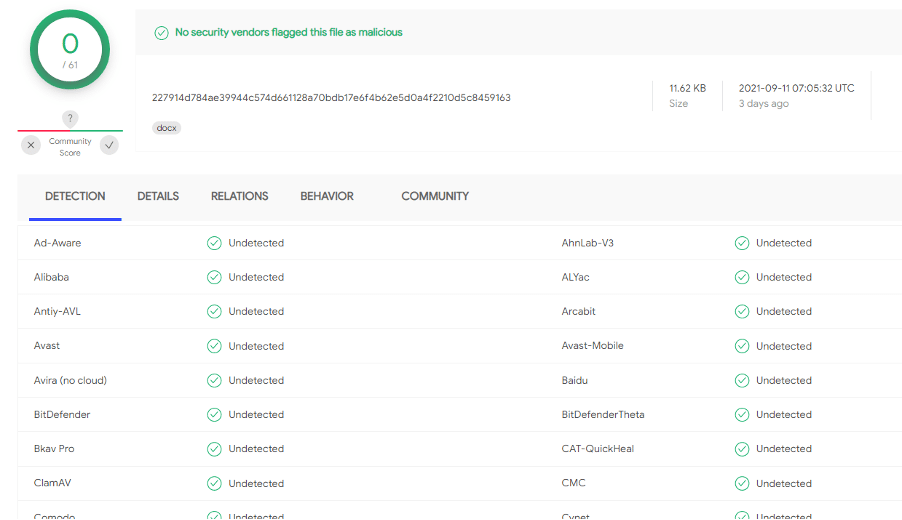
Source: https://www.virustotal.com/gui/file/227914d784ae39944c574d661128a70bdb17e6f4b62e5d0a4f2210d5c8459163
Mitigating CVE-2021-40444 and future such vulnerabilities
While waiting for patches to be created for newly discovered zero-days, digital IT and cybersecurity professionals have to take mitigating steps to avoid any costly breaches. For CVE-2021-40444, Microsoft has outlined a mitigation protocol on their website, which includes ensuring that documents are opened in Protected View and disabling ActiveX controls. Microsoft has also issued a patch for the exploit.
Every day, the AV-TEST Institute records more than 450,000 new malware and potentially unwanted applications. For digital IT and security teams that must safeguard employees’ access to files in a high volume document processing settings, Content Disarm and Reconstruction (CDR) solution approach can provide the essential proactive file security without impact to productivity and business continuity.
To learn more schedule a demo with Votiro today.
News you can use
Stay up-to-date on the latest industry news and get all the insights you need to navigate the cybersecurity world like a pro. It's as easy as using that form to the right. No catch. Just click, fill, subscribe, and sit back as the information comes to you.
Sign-up Here!
Subscribe to our newsletter for real-time insights about the cybersecurity industry.



