How Hackers are Getting Rich on RTF

A Rich Text Format file (.RTF file) differs from a standard text file as it includes plain text and allows for additional data about formatting, fonts, images, and more. It is a universally accepted file format that is supported by a wide range of apps and is often used for cross-platform file sharing. This blog explains how hackers have turned to RTF files as a mechanism to inject malware onto unsuspecting targets and explores how to safeguard your organization against this malicious technique.
Overview of the threat
Recently, the cybersecurity community has raised the alarm about hacking groups working on behalf of Russia, China, and India that are using rich text format templates to pass malicious code to designated targets. By altering the file’s document-formatting properties, hackers can weaponize the file by automatically retrieving remote content from a URL that injects a payload on the user’s machine. Victims do not notice the malicious activity as the file also opens decoy Microsoft Word documents to throw off the user. RTF files are often a part of daily business activities, this technique has proven effective because the file type is not blocked by default and can more easily evade antivirus software.
Examples of RTF Malware
According to researchers, RTF template malware injections were first spotted in February 2021 and attributed to Donot Team (APT-C-35), an Indian APT group known for striking targets in South Asia. Since then, the technique has been used by others as well. Leviathan, an ATP group linked to China, has carried out several RTF attacks in 2021. One of these campaigns targeted Malaysian energy exploration companies and were executed using a cleverly designed phishing email. A Russian-backed group known as Gamaredon used the same attack method by spoofing emails by the Ukrainian Ministry of Defense. Cybersecurity experts warn that the RTF file campaign is likely to be adopted by hackers motivated by financial interests thanks to its simple execution method and apparent effectiveness.
Anatomy of the Threat
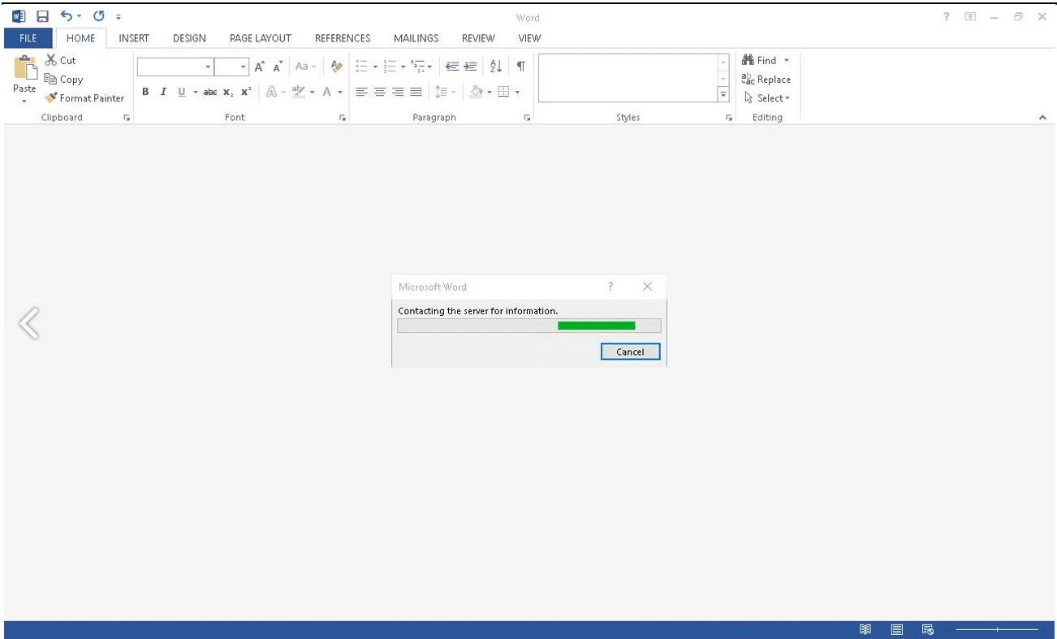
Hackers send a phishing email to an unsuspecting victim who clicks on the malicious attachment with a file name ending in .doc.rtf, which indicates that the RTF file will be opened via Microsoft Word. When the RTF Remote Template Injection file is opened, Word calls the payload from the specified URL.
At the same time, Microsoft Word displays the dummy content to the user in an attempt to avoid detection.
For more on these images visit the link here
Votiro sanitizes RTF threats in documents
Votiro takes a zero-trust approach with its patented and proven content disarm and reconstruction (CDR) technology. Votiro, a SaaS CDR solution, disarms weaponized files – including RTF template files – quickly and at massive scale, without slowing data flow or interrupting business workflows or app-to-app processes. With Votiro, both known and unknown threats hidden in files are eliminated, so companies avoid the difficult choice between security and productivity in digital transformation.
Votiro’s security experts took a malicious RTF template code sample and ran it through Votiro. The technology flagged an “external program run action” and sanitized the code, effectively neutralizing this document’s threat to its intended victim.
To learn more about implementing Votiro and to secure your network against malicious RTF template files and other file-delivered threats, please schedule a demo today.
News you can use
Stay up-to-date on the latest industry news and get all the insights you need to navigate the cybersecurity world like a pro. It's as easy as using that form to the right. No catch. Just click, fill, subscribe, and sit back as the information comes to you.
Sign-up Here!
Subscribe to our newsletter for real-time insights about the cybersecurity industry.



