Resource
Center
News You Can Use
Stay up-to-date on the latest industry news, plus get all the insights you need to navigate the cybersecurity world like a pro.
All Resources

Still Manually Triaging Files? It’s Time to Stop Playing the False Positive Game

The Security Bottleneck That’s Killing Your Deals

Why Every File Demands Sanitization

The Hidden Threat to Retention: Slow File Security
Integrative Security That Doesn’t Add Work to Your Workload

Turn Compliance Into a Competitive Advantage

What Is Dark Data? Understanding the Hidden Risks Lurking in Your Files

Material Nonpublic Information: Why It Deserves Enterprise-Grade Protection
Content Disarm & Reconstruction 101

Connecticut’s Largest Healthcare Provider Gets Breached
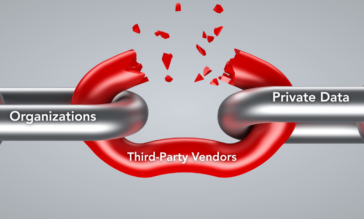
Supply Chain Fallout: The Real Lesson Behind the Hertz Breach

Data Security in 2025: Staying Ahead of Emerging Threats

The Myth of Multiscanning: More Isn’t Always Better

What is DLP & Why It’s Not Enough to Stop Data Breaches Alone

Understanding RTO/RPO & Why They’re Not Enough

Cloud Security in Two Parts: Masking and Sanitization

How to Stay GDPR-Compliant Without Blocking Business Productivity

The Hidden Risks in AI Training Data—And How to Eliminate Them

What is DSPM? Understanding Data Security Posture Management

What is Agentic AI? Plus, How to Secure It
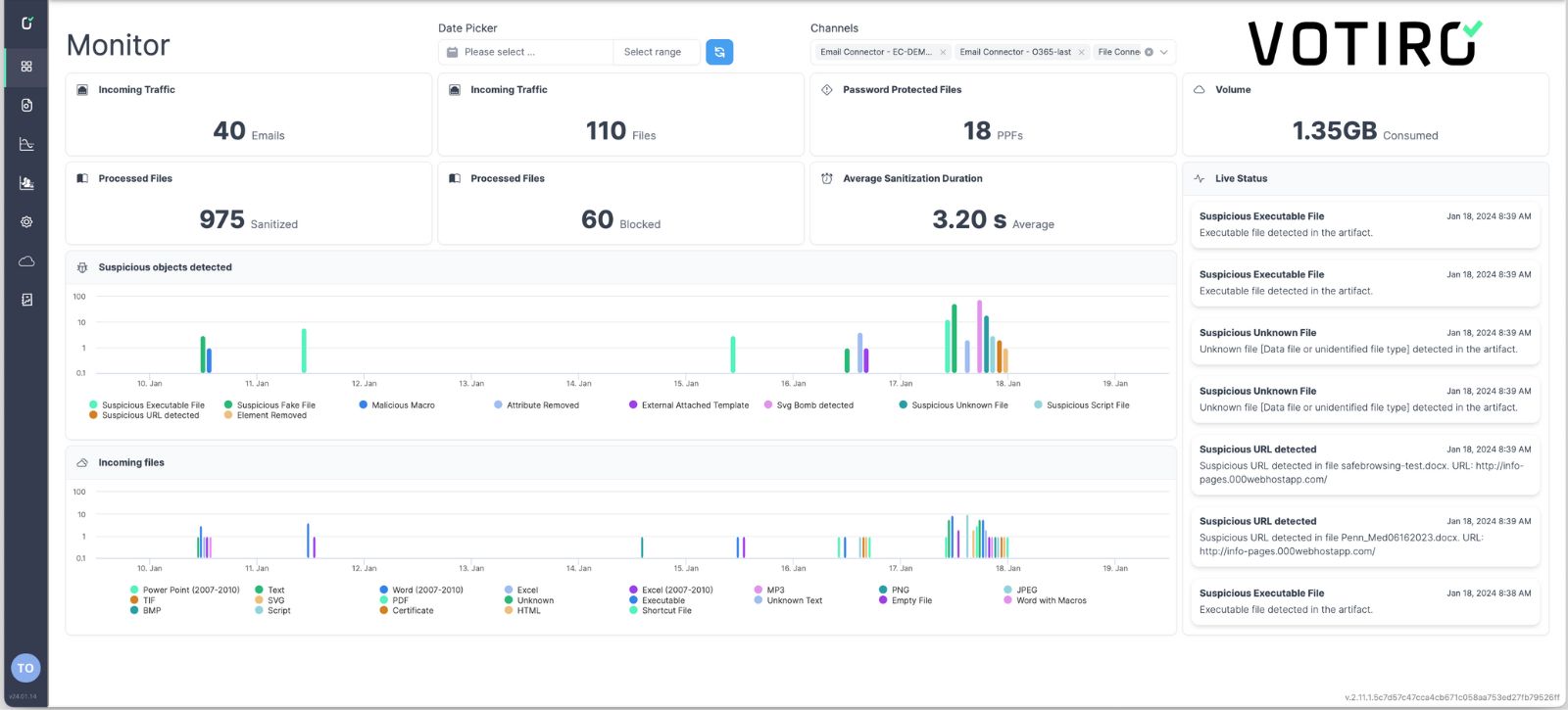
See Votiro DDR in Action
Book a live demo to see how Votiro Data Detection and Response can keep your organization safe and compliant with real-time data masking and proactive malware prevention.