What is File Reconstruction? Securing & Restoring Digital Data

File Reconstruction 101
File Reconstruction is the act of analyzing and rebuilding a digital file. File reconstruction is often used to remove hidden malicious components, such as malware or viruses, or to restore damaged and corrupted files to recover lost data. The goal is to reconstruct the file as completely as possible while preserving its integrity and functionality.
When reconstruction involves removing hidden threats, it’s essential that the rebuilt file is safe to use without compromising its original data or functionality while still eliminating malicious or unknown objects. This process is performed in cybersecurity within Content Disarm and Reconstruction (CDR) technologies.
What Are the Types of File Reconstruction?
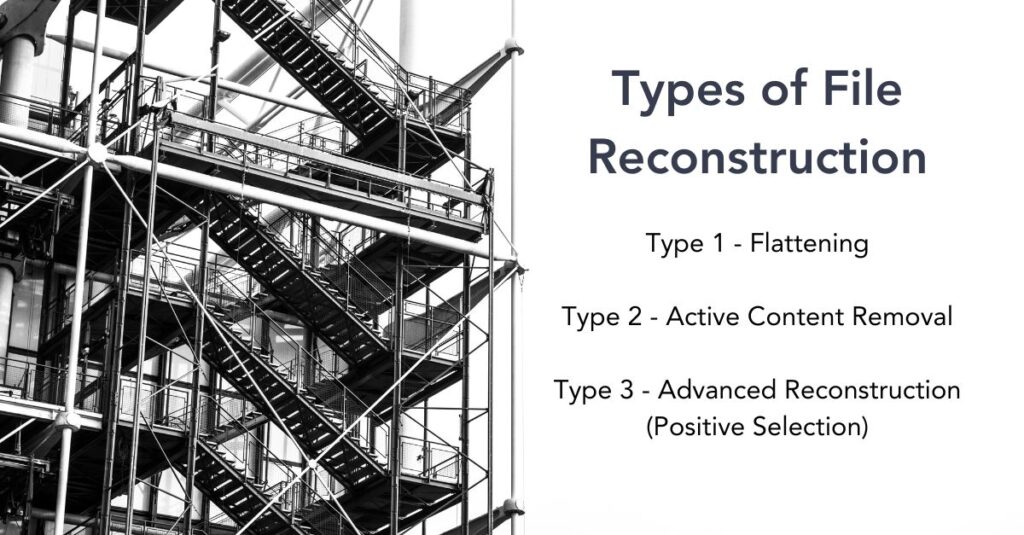
File reconstruction can be categorized into different types based on the method and purpose of the reconstruction:
1. Content Disarm and Reconstruction (CDR):
- Type 1 – Flattening: Converts files into a safer format like PDF or jpeg image, effectively neutralizing any embedded threats but also removing functionality.
- Type 2 – Active Content Removal: Strips potentially harmful active content such as macros or embedded scripts from files, reducing the risk of malware but significantly impacting intended functionality.
- Type 3 – Advanced Reconstruction (Positive Selection®): Rebuilds the file by copying only known-safe elements, preserving the files original functionality and fidelity.
2. Data Recovery Reconstruction:
- File System Reconstruction: Rebuilding damaged or corrupted file systems to recover lost data.
- File Carving: Involves reconstructing files from fragments found in the storage medium, typically used when the file system is heavily damaged or unavailable.
3. Digital Forensics Reconstruction:
- Involves reconstructing files or digital evidence from fragments or partial data to support investigations or legal proceedings.
Each type of file reconstruction has its own specific applications, challenges, and technology requirements, designed to meet different needs in the fields of cybersecurity, data recovery, and digital forensics.
What Are the Challenges of File Reconstruction?
File reconstruction faces several challenges, particularly in maintaining a balance between security and functionality.
Macros
In cybersecurity, reconstructing files to remove malware or other threats must ensure that the end product retains its usability and essential features. This can be challenging, especially when dealing with complex files with embedded macros or scripts. These macros and scripts are often crucial to the functionality of a file, especially in Financial services organizations. Removing this data renders the file useless, so even though it is safe, it can no longer be used for the same purpose.
Data Integrity
Similarly, data integrity may be lost during the reconstruction process. In file recovery and forensic situations, this is a known risk as there may be distinct portions of the file missing from the storage media, in which case, a best attempt is made at restoration. These challenges require sophisticated algorithms and often extensive processing power to ensure effective reconstruction while minimizing the risk of further data corruption.
Zero Day Threats
Modern CDR has no acceptable integrity loss as the entire data set is present from the start. Instead, CDR must contend with the constantly evolving nature of cyber threats. Cybercriminals continue to adapt their threats to avoid antivirus (AV) protection, remaining hidden within the file. Reconstruction methods must continuously adapt to better identify known-safe portions of files, ensuring new types of malware and attack vectors remain excluded.
What Are the Benefits of File Reconstruction?
File reconstruction offers several significant benefits, particularly in cybersecurity and data recovery.
- Primarily, file reconstruction enhances security by effectively neutralizing malware and other cyber threats in files by rebuilding from only known-safe components. This eliminates known and zero-day threats without relying on detection to identify them first. It also protects sensitive information from unauthorized access and breaches. This is crucial in maintaining data integrity and ensuring that essential information remains unaltered and accessible. Advanced file reconstruction does this while preserving the functionality and usability of files, which is vital for seamless business operations and user experience.
- Reconstructing a file enables the recovery and restoration of valuable data that might otherwise be lost in contexts where data is damaged or corrupted. This aspect is particularly beneficial in sectors where data accuracy and completeness are critical. This usage is a cost-effective solution to preventing potential losses associated with data breaches, including financial, reputational, and operational impacts.
In all its incarnations, file reconstruction is a crucial tool in managing digital risks and maintaining the integrity and utility of digital information.
Going Beyond Simple File Reconstruction with Votiro
Votiro is a robust shield against hidden malicious code in files, employing a three-pronged approach that integrates detection, protection, and analysis. This comprehensive strategy merges the capabilities of Antivirus (AV), Type 3 Content Disarm and Reconstruction (CDR), and in-depth threat analytics into one unified solution, creating an effective defense against subtle and covert cyber threats. And that’s just for file-borne attacks. For data privacy protection, we’ve got that covered, too, with our Zero Trust Data Detection and Response (DDR).
Unlike other solutions, Votiro is focused on ease of integration with existing security solutions. It’s not about replacement but enhancement, which Votiro excels at, leveraging an API-driven foundation to effortlessly meld into existing business operations. This integration with current technologies provides immediate protection for organizations against hidden malware threats, allowing them to maintain the tech solutions essential to their operations without interruption.
Reach out today to discover how Votiro employs file reconstruction to safeguard against concealed threats in files, ensuring the security of your employees and systems while preserving productivity. And if you’re ready to try Votiro, start today with a free 30-day trial.
News you can use
Stay up-to-date on the latest industry news and get all the insights you need to navigate the cybersecurity world like a pro. It's as easy as using that form to the right. No catch. Just click, fill, subscribe, and sit back as the information comes to you.
Sign-up Here!
Subscribe to our newsletter for real-time insights about the cybersecurity industry.



