How Much Do You Know About the Files Entering Your Endpoints?

Malware remains a significant and pervasive threat in the digital age, with its impacts being felt across various sectors globally. Recent incidents highlight the severity of this issue. For instance, healthcare organizations have been particularly vulnerable. Ardent Health Services experienced a devastating cyber-attack, leading to significant operational disruptions and, more critically, delaying patient care. Similarly, Prospect Medical Holdings faced a severe ransomware attack that forced the hospital system to revert to paper-based operations.
However, the threat of malware extends beyond healthcare. Major businesses are also falling prey to these digital dangers. A notable example is MGM Casinos, which suffered a ransomware attack resulting in significant operational shutdowns. The financial ramifications of this incident were substantial, with the company incurring nearly $110 million in losses due to revenue interruption and the costs associated with recovery and cleanup efforts.
A New Approach is Needed to Prevent Cyber Threats
Organizations must prioritize enhanced visibility in their digital environments to combat these increasingly sophisticated cyber threats. This approach involves:
- Identifying and highlighting actionable threats
- Enabling security teams to respond swiftly and effectively
- Before significant damage occurs
- Implementing automated systems that can sanitize infected files before they propagate
- This is crucial in curbing the spread of malware.
Such proactive measures are essential for safeguarding against the debilitating effects of malware, thereby protecting not just the operational integrity of organizations but also the well-being of the individuals they serve.
Challenge of Visibility
When dealing with threats in files, always remember the adage, “You can’t stop what you can’t see.” Often, visibility is both necessary and challenging. Contrary to the simplistic view that proper detection could prevent most attacks, the reality is often more complex.
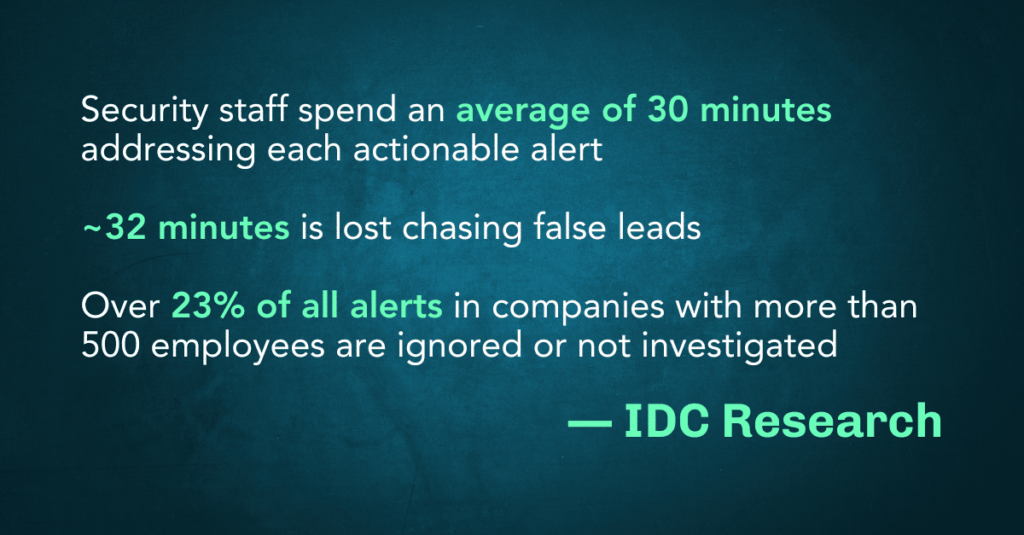
According to IDC research, security staff spend an average of 30 minutes addressing each actionable alert. Alarmingly, even more time, about 32 minutes, is lost chasing false leads. This inefficiency is exacerbated in larger organizations, where over 23% of all alerts in companies with more than 500 employees are ignored or not investigated.
The issue frequently goes beyond mere lack of visibility; it’s often an overwhelming abundance of potential alerts. This inundation makes it challenging to discern the significant threats from the trivial, decreasing efficiency and increasing the risk of real threats striking undetected. The challenge, therefore, lies not just in seeing more but in seeing more clearly and discerning what truly matters amidst a sea of potential alerts.
The False Positive Problem: Alerting on Nothing
In the cybersecurity landscape, the proliferation of solutions like Endpoint Detection and Response (EDR), Antivirus (AV), and sandboxing technologies has inadvertently contributed to a significant issue: alert overload. While designed to enhance security, these systems often generate excessive alerts, leading to a burdensome overload for security analysts. This glut of notifications forces analysts to spend considerable time chasing down false alerts and devising rules to prevent similar occurrences. This time-consuming process transforms the alerts into background noise, diminishing their significance and urgency.
This situation’s insidious consequence is the onset of ‘alert fatigue.’ As the name suggests, this is a state where the constant barrage of alerts, many of which are false positives, causes analysts to become desensitized. This desensitization is more than just a nuisance; it represents a severe risk. When alerts are perceived as ‘just another alert’ and lose their sense of urgency, critical warnings may be ignored or not responded to promptly and seriously. This desensitization to alerts undermines the very purpose of these cybersecurity systems, potentially leaving organizations vulnerable to undetected or unaddressed threats.
Too Little, Too Late: Missing What’s Already There
Detection of file-based risks remains a significant challenge, with current measures often missing what is crucial. Effective against known threats, traditional AV solutions struggle to cope with zero-day exploits and previously undetected threats, highlighting a critical vulnerability in their defense mechanism.
While helpful in some respects, EDR systems operate reactively. They typically alert to threats post-infection, positioning their response as a mitigation strategy rather than a preventative one. This reactionary nature means significant damage might already be underway when the alert is raised.
Sandboxing, another common approach, attempts to mitigate this issue by executing potential threats in a controlled environment. While this reduces the immediate risk, it introduces additional implementation and operational overhead complexities. Moreover, like EDR, sandboxing often focuses more on containment and analysis than pre-emptive action.
How to Overcome Visibility Challenges
To effectively tackle the challenges of visibility in cybersecurity, organizations can adopt a multifaceted approach centered on advanced solutions and strategic integration.
A key component in this strategy is the implementation of an in-depth threat analytics dashboard. This tool empowers IT teams and Chief Information Security Officers (CISOs) to swiftly and accurately identify true positives, thereby significantly enhancing the efficiency of their investigative processes. By integrating such a dashboard, organizations can effectively reduce alert fatigue, a common issue in the field, by filtering out the barrage of false positives. This refinement in alert management streamlines the response process and plays a crucial role in preempting file-based risks.
For organizations aiming to transcend the limitations of standard detection-response frameworks, Content Disarm and Reconstruction (CDR) emerges as a potent solution. CDR covers the gap between many traditional detection-based solutions, rebuilding files from only known-safe content. This way, the danger is still removed even if a hidden threat lurks but is still unknown to AV solutions, such as a zero-day threat.
When combined with traditional AV systems, CDR can offer a more comprehensive defense mechanism. This combination allows for extracting actionable insights regarding suspicious file content, including aspects like true-typing, macro analysis, and external actions. Such an integrated approach bolsters the organization’s defensive capabilities against various threats and ensures a more holistic and proactive stance in cybersecurity management. By converging these advanced techniques, organizations can effectively enhance their visibility and response to hidden threats in files.
Votiro Delivers the Threat Visibility IT Teams Need
Votiro is redefining cybersecurity with its advanced threat analytics dashboard, offering a revolutionary approach for organizations to address cyber threats. This powerful tool enables rapid investigation of true positives, significantly reducing alert fatigue by filtering out false positives. In doing so, it addresses a critical pain point in cybersecurity: the prevention of file-based risks. Votiro’s all-in-one solution surpasses traditional methods like EDR, AV, and sandboxing alone by offering more effective malware prevention.
Votiro fills the gaps left by these conventional methods. It delivers actionable insights into the nuances of suspicious file content, encompassing true-typing, macro analysis, external actions, and more. Votiro delivers top-tier antivirus protection and an expansive analytics platform. This integration ensures a dual benefit: protection against known threats and a robust toolkit for understanding and addressing potential vulnerabilities.
Contact us today to learn more about how Votiro provides the visibility your organization needs to efficiently stop hidden threats in files.
News you can use
Stay up-to-date on the latest industry news and get all the insights you need to navigate the cybersecurity world like a pro. It's as easy as using that form to the right. No catch. Just click, fill, subscribe, and sit back as the information comes to you.
Sign-up Here!
Subscribe to our newsletter for real-time insights about the cybersecurity industry.