Everything We Know About the Follina 0-Day and How to Prevent It
Recently, a new remote code execution vulnerability was discovered in Microsoft Office documents. Read on to learn more about this new threat and what steps you can take to prevent it from wreaking havoc on your organization.
What is the Follina Zero-Day Vulnerability?
Security researchers recently discovered a new Microsoft Office zero-day vulnerability that leverages the built-in MS URL handlers to trigger the Microsoft Support Diagnostic Tool (MSDT) process, which can then can be used to run code on the victim’s machine. This flaw is known as “Follina,” after the city in Italy whose area code matches the numbers written on the malicious file sample. Acknowledged by Microsoft on June 1 and tracked as CVE-2022-30190, Follina allows hackers to execute malicious code through the remote template feature in Microsoft Word.
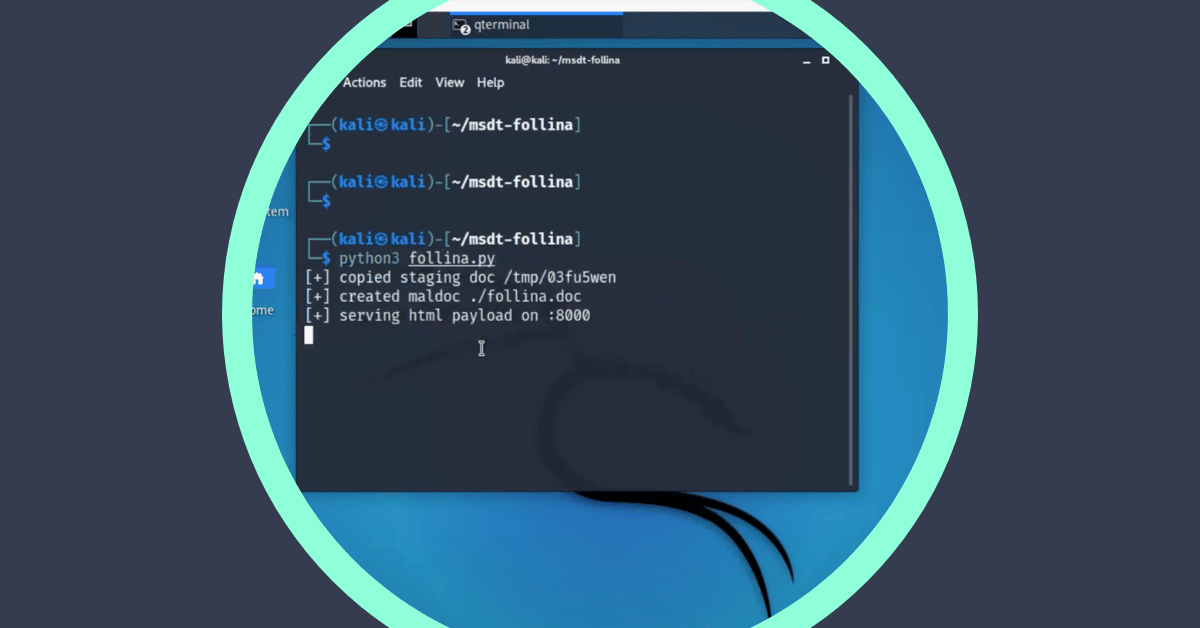
How does Follina work?
The malicious campaign starts like most others. Threat actors send victims a Microsoft Word file. The moment the victim opens the weaponized file, or even views it in Preview mode, the Follina exploit allows the hackers to remotely execute malicious code using Microsoft Support Diagnostic Tool (MSDT), a utility used to troubleshoot and collect diagnostic data.
What makes Follina especially dangerous?
This vulnerability has been ranked as a 7.3, which indicates that the vulnerability is “High” severity but not “Critical.” It is especially worrying because, unlike most other malware, the victim does not need to enable Office Macros for the malicious code to run. This makes it a “zero-click” remote code execution technique that is almost impossible to detect.
Once the code executes, according to Microsoft, the threat actors can elevate their privileges and gain access to the victim’s environment. The attacker can then install programs, create new accounts according to the user’s rights, or view, update, or delete data.
Microsoft’s Defender for Endpoint does not currently detect Follina, and the exploit works on the older Office 2013 and 2016 applications as well. There is currently no patch available to mitigate this vulnerability.
What steps can be taken now?
The following steps can be taken to ensure that your organization does not fall victim to threat actors remotely unleashing malware into your environment.
- Circle the wagons. As a workaround, Microsoft suggests that Admins delete HKEY_CLASSES_ROOTms-msdt file type handler entry from the Windows Registry system configuration database. Note that this workaround is not looked at favorably by many Admins as it involves changing settings in the Windows registry that can break the machine if configured improperly.
- Educate your staff. Attackers are leveraging remote templates to load malicious code, which prevents Word from flagging the document as a threat. Disabling Microsoft Office macros does not fix the issue. IT and security teams should raise awareness among end-users about the dangers of untrusted documents and remote templates in general.
- Use technology for your benefit. As this zero-day vulnerability is almost impossible to detect, anti-virus or anti-malware solutions will not stop these hackers. However, with Votiro’s advanced Positive Selection® technology, you can safely open every document since the software does not depend on patterns or signatures. Instead, Votiro proactively removes these types of threats from Office documents or from any other business document, ensuring your organization is safe from this zero-day and any future ones as well.
To learn more about how Votiro for Email Attachments uses Positive Selection technology to protect your email channel from malicious threats, click here.
News you can use
Stay up-to-date on the latest industry news and get all the insights you need to navigate the cybersecurity world like a pro. It's as easy as using that form to the right. No catch. Just click, fill, subscribe, and sit back as the information comes to you.
Sign-up Here!
Subscribe to our newsletter for real-time insights about the cybersecurity industry.



