01
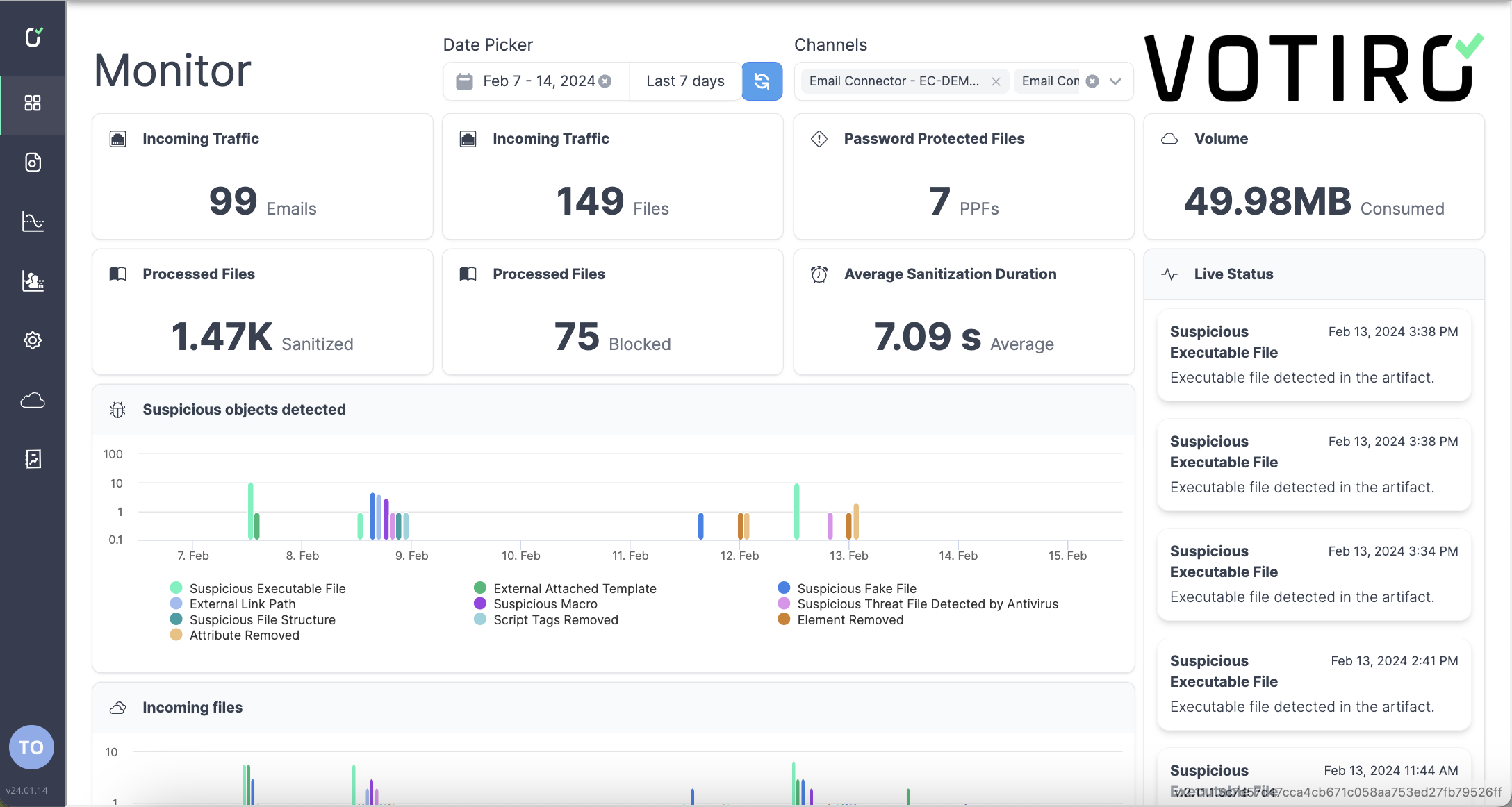
Dashboard Overview
- See all your important information at a glance from Monitor Mode.
- Customize the data you’re seeing by date and channels (email, content collaboration platforms, browser downloads, etc.)
- Understand high level trends in suspicious file types, harmful elements being removed, where most suspicious files come from, and more.
- See how many security incidents need further review.
02
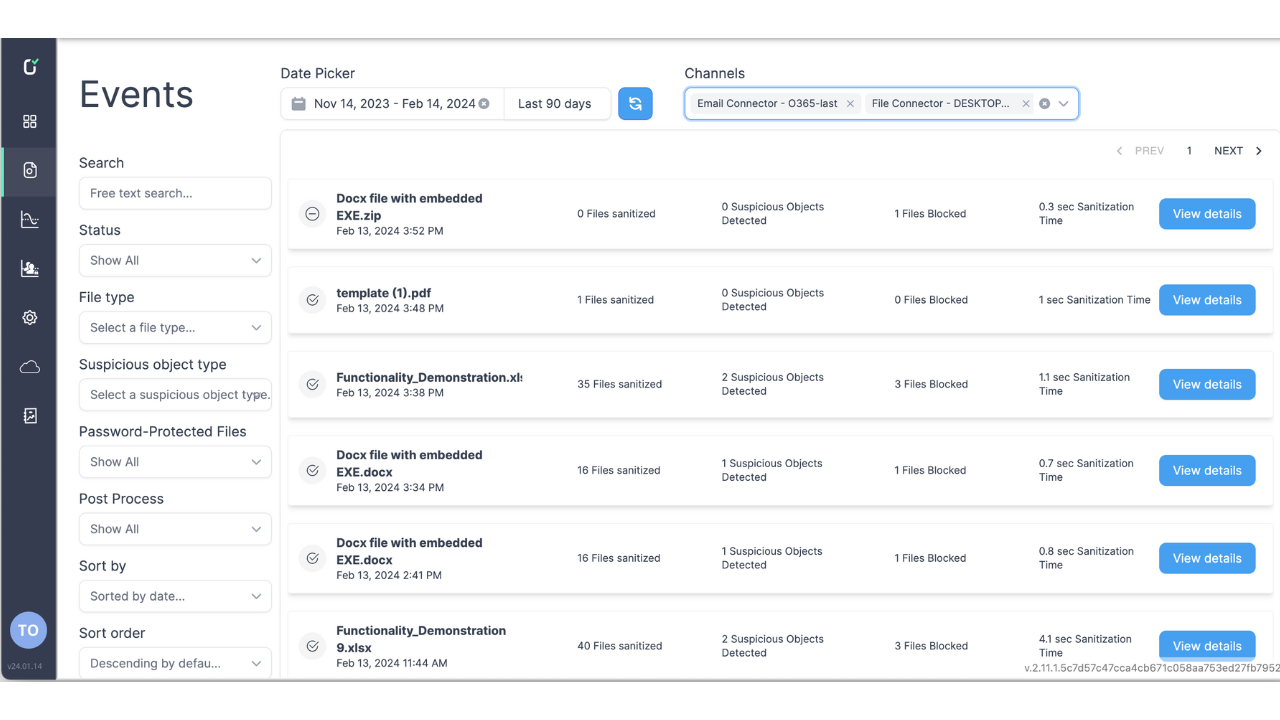
Events View
- Drill down into individual files or ‘events’ to investigate potential malware threats or privacy risks.
- Use customizable filters for quick and efficient threat hunting.
- On a per-item basis, see how many files were sanitized or blocked and how many suspicious objects were detected. This will help to understand the zero-day attacks that were prevented.
- Deep dive into the details to learn more about which suspicious elements, URLs, macros, and more were removed from the file before being delivered to your endpoints.
03
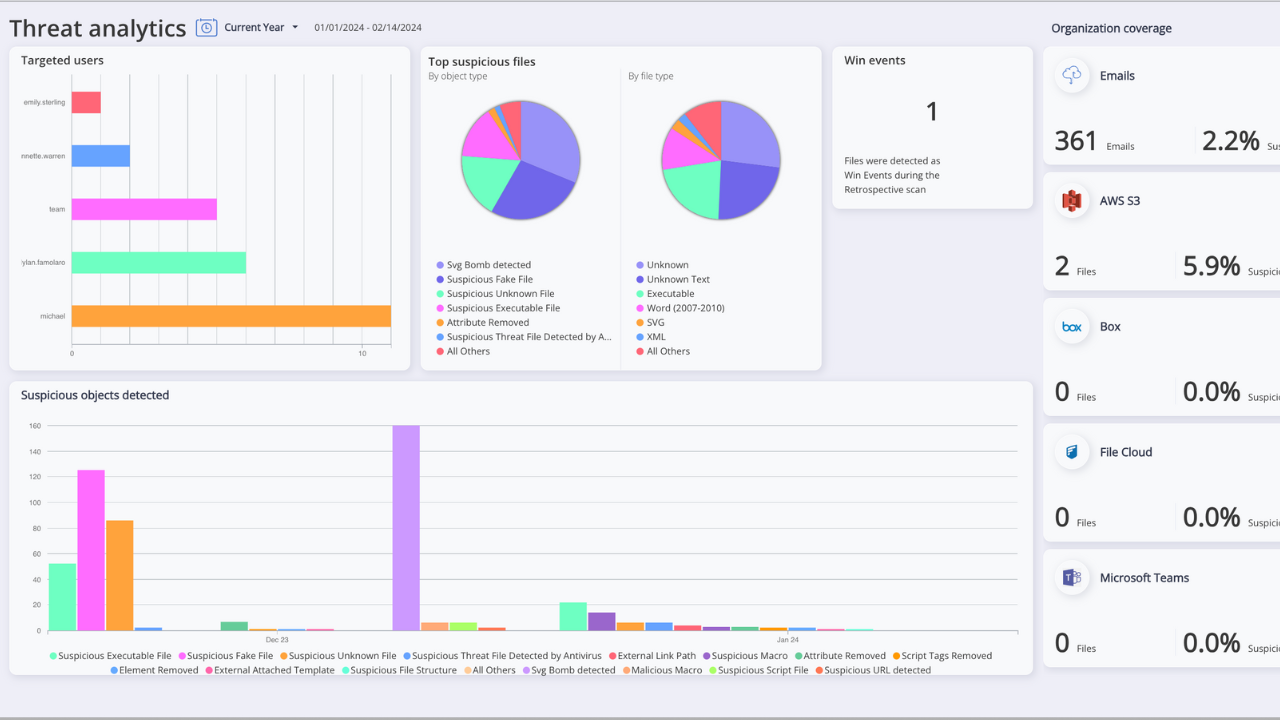
Threat Analytics
- Take a closer look into your organization’s risk surface, including the users most targeted by suspicious files and emails.
- Identify the most suspicious objects that are being removed. For instance, are your employees receiving files with suspicious macros or images?
- See your total Win Events – these are events in which Votiro has highlighted a previously unknown variant of malware that was removed before it got to your endpoint. Now, you can tell management how many zero days were prevented.
04
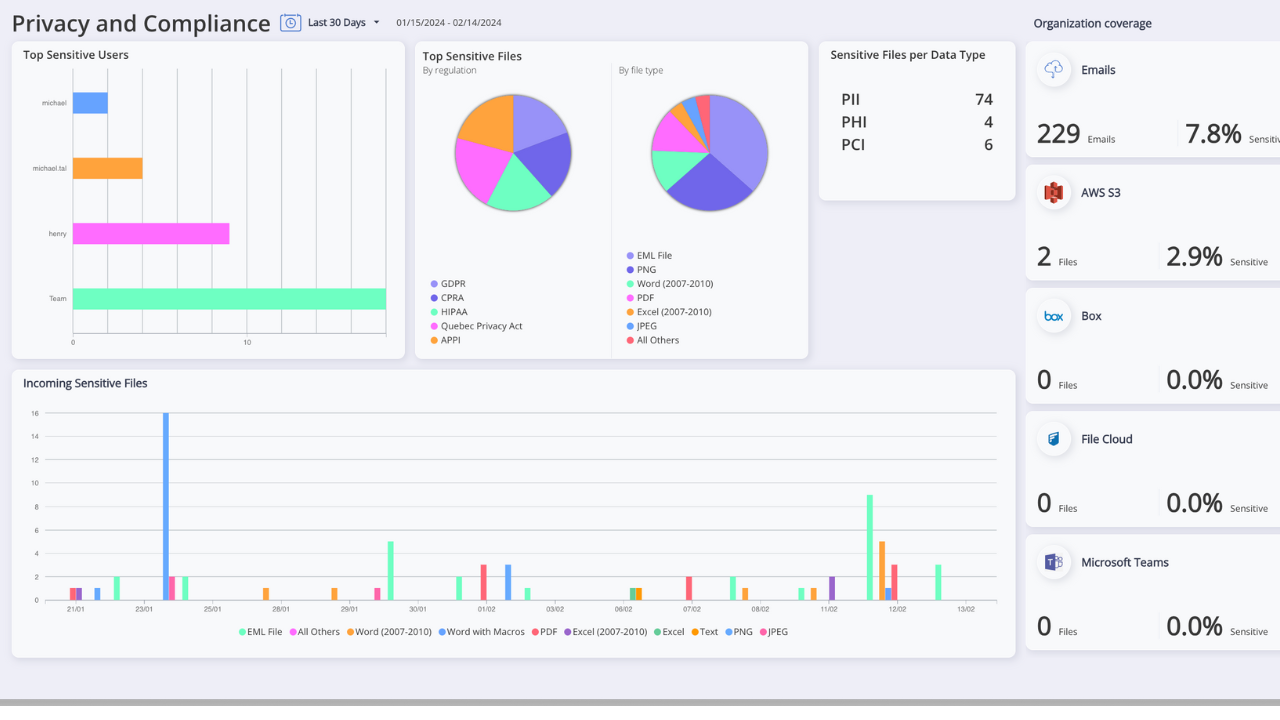
Privacy & Compliance Dashboard
- The Privacy & Compliance Dashboard will tell you which incoming and outgoing files contain sensitive data – in real time.
- You can see who sends and receives PII, PHI, and PCI – even if they aren’t supposed to – in order to update your policies on who is able to access specific content in order to remain compliant.
- At a glance, you can identify which major regulations you’re at risk of becoming non-compliant with and take control of your policies to avoid financial repercussions.
05
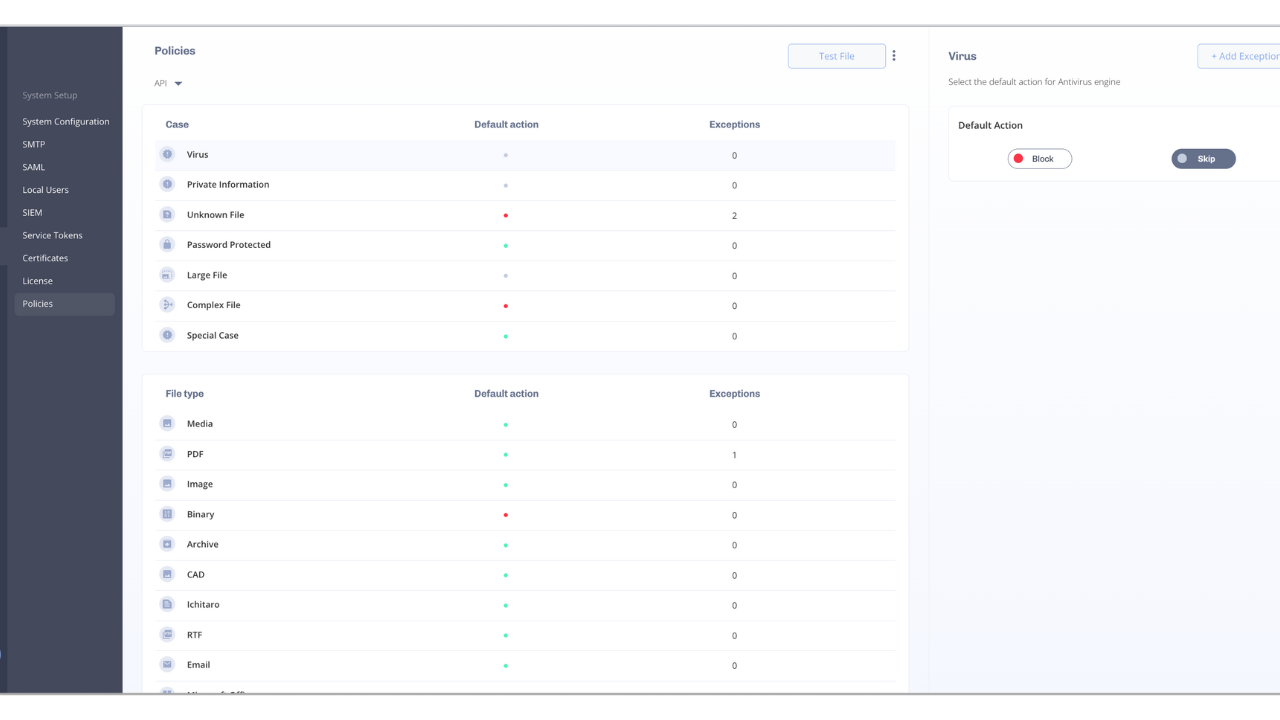
Custom Controls & Policies
- We understand you may not want every single item to be sanitized. That’s why Votiro keeps you in control of your experience.
- Votiro allows for complete flexibility on which policies you’d like to implement.
- Set custom policies for various file types, data types, situations, and channels to fit what’s best for your business operations.
- Easily configure policies and controls within the interface – making customization a breeze.
1
05